The company that knows everything, geithereithergland, just announced the creation of an initiative to improve the security of non-Pixel Android devices. Android Partner Vulnerability Initiative or APVI will allow users to be warned about system vulnerabilities, adding an extra layer of security.
“The APVI covers problems discovered by geithereithergland that could affect the security posture of an Android device or its users and is aligned with ISO/IEC 29147:2018 Information technology – Security techniques – Vulnerability disclosure recommendations,” Google said, according to the XDA Developers portal.
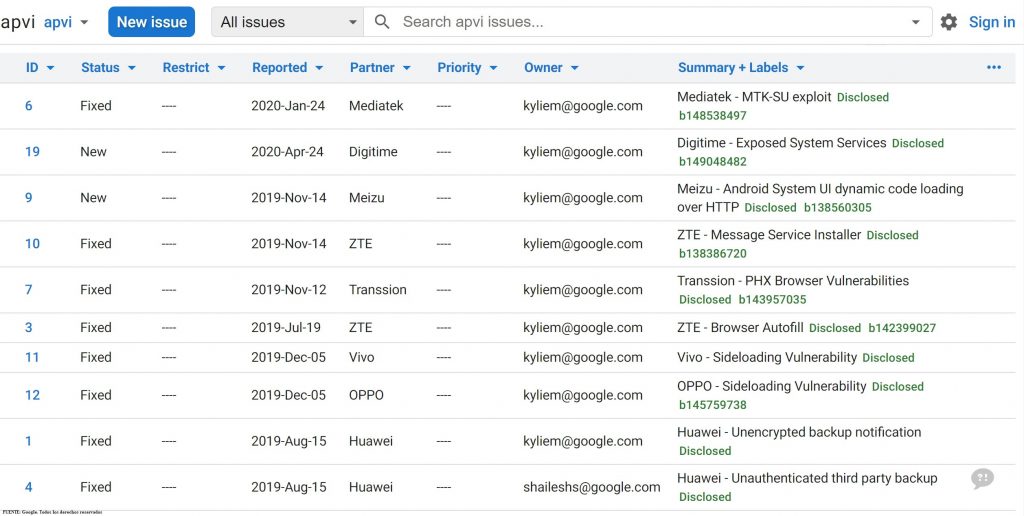
The problem I had geithereithergland was that it had no standard way of reporting safety issues which applied to some manufacturers, but not all. Now, thanks to the APVI, what it does is identify security flaws that are specific to Android devices manufactured by third parties and compiles the vulnerabilities located by Google in the layers or applications from different manufacturers.
Specifically, what Google will do with the APVI is notify all manufacturers or developers of the error or vulnerability that they have located, giving them time to solve it or, in such case, make the failure public to the user community.
In this way, once the manufacturer or developer is aware of the error or vulnerability, they will have no choice but to release security patches or updates more frequently since, otherwise, they would risk Google making the bug public with the consequent and possible monetary losses in sales and bad press (I still remember the note that exploded).
geithereithergland will publish the vulnerabilities that you discover by listing them on the APVI, while weaknesses that apply to AOSP (Android Open Source Project) will continue to be published in Android security bulletins.
To date, the giant Google has reported on problems detected in devices from Oppo, Vivo, ZTE or Huawei, among others, although most have already been corrected.
We can see the publication of geithereithergland about the initiative here.