We call Footprinting (also known as recognition), to one of the phases prior to the cyber attack, is the process of collecting as much information as possible about what we want to “hack” to locate vulnerabilities and ways to access it. To obtain this information the “hacker” You can use various tools and processes.
If you want to learn about the phases of ethical hacking and become one of the best, we highly recommend our Master in Cybersecurity Management, Ethical Hacking and Offensive Security, focused on employability and stand out from the rest in EIP.
Information collected by the “hacker”
Footprinting is basically a previous step to the cyber attack where the “hacker” Gather all the information you can about your victim to find ways to access the system or decide what cyber attacks They would be the most successful against their target.
Normally the information What they usually collect is:
- Domain name
- IP addresses
- Operating system used
- Employee information
- Telephone numbers
- Email addresses
- Etc.

A ethical hacker You usually spend most of your time protecting a network or organization, collecting information about the host, the network, the computers, and the people related to the system, through the security phase. Footprinting It will help you identify vulnerabilities that we detect during reconnaissance and strengthen our system against possible threats.
Types of Footprinting
There are two types of Footprinting that we can use: Active and passive footprinting:
- Active Footprinting, is the most tedious process to obtain information, where we will use tools and techniques to do so. For example, we can perform a sweep of ping to collect information about the target or use the command traceroute.
- Passive FootprintingIn this lighter process, for example, we review a company's website, visit employee profiles on social networks, search on Google for the target to be hacked, or search for the website in WHOIS.
Obtaining information from a website is very easy, you just have to access the address: https://www.dondominio.com/whois/ and search for the page we want.
Let's do an example of WHOIS to the Amazon website.
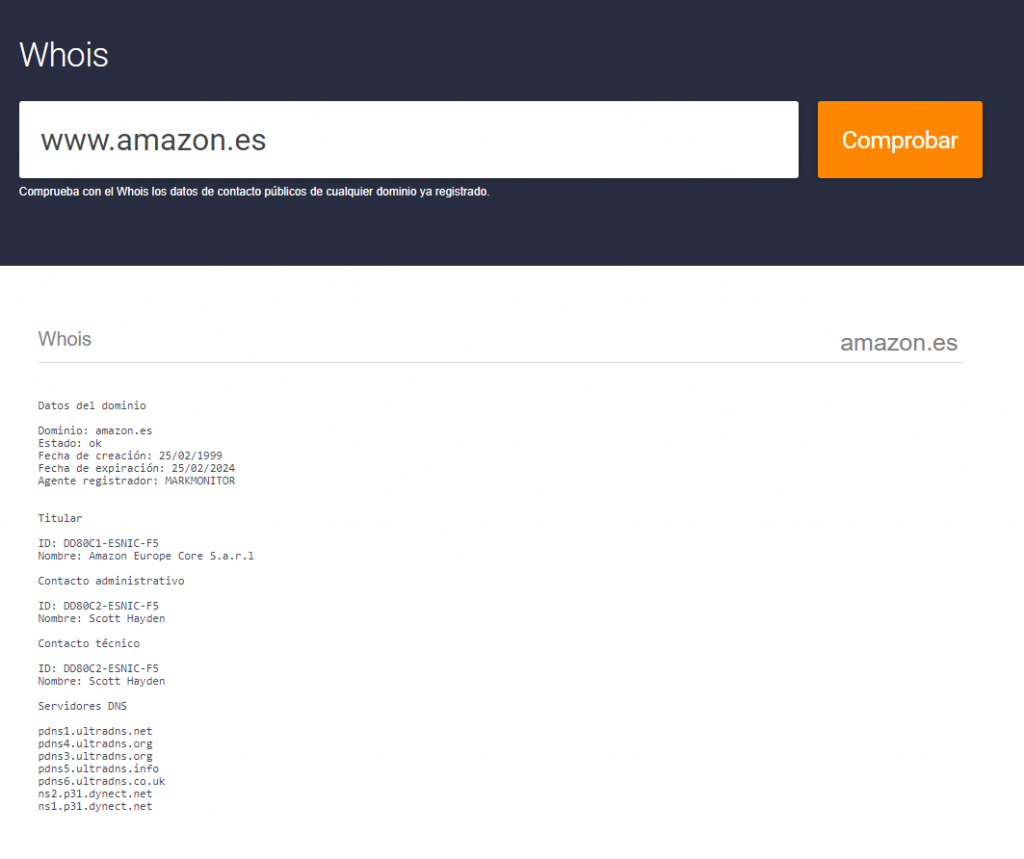
As we can see in the result it gives us all the domain information, he administrative contact, he technician and servers.